Kubernetes is the go-to container management tool for most businesses at the enterprise level. But there are so many pieces that come into play, security can be a problem. Not only do you have to make sure your container system deployed on the established security controls, but you also have to deploy people and pods containers with a tight eye on security. If not, you run the risk of data theft and other losses.
For that, you must use every caution when deploying a cluster you can Kubernetes you. One thing that should be considered a must is the security policy pod. I want to walk you through the basics of creating a security policy pod Kubernetes. You can secure Kubernetes using Pod Security Policy Admission Controller.
The Pod Security Policy
With Pod Security Policy, administrators can control security Kubernetes specification pod. Security pod Policy is a configuration that determines the specific security conditions pod must meet in order to be accepted in a cluster.
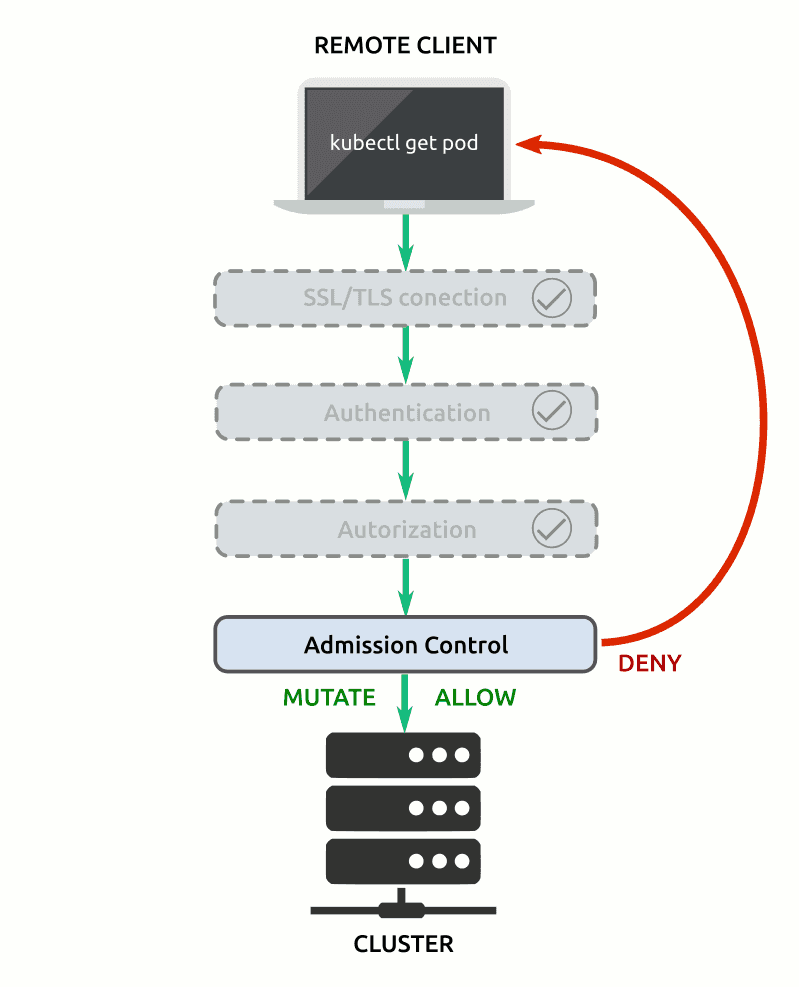
If the conditions are not met, said the pod will be rejected. By utilizing PodSecurityPolicy definition of the object, it is possible to control such people:
- Pod ability to run a special container
- Pod ability to use privilege escalation
- Pod access to that kind of volume
- Pod access to the host file system
- Use of this pod host network and configuration objects
Creating a Security Policy Pod Kubernetes
Pod security policies defined in YAML files. YAML file that is then applied, with the help of kubectl command, to determine the new policy.
Let us create a new security policy pod. This policy will do the following:
- Disabling the pod's ability to run a special container
- Allows the use of SELinux
- Allows the use of the Linux group
- Allows users to run the entry point of the container with a different user name

